
From Ambiguity to Attribution: NATO’s New Language of Deterrence
NATO is no longer tiptoeing around its enemies. The alliance now speaks and acts with a clear and distinct intention.

The Costs of Espionage
States spend a lot of time worrying about spies, and a lot of money trying to protect themselves from espionage. They construct multilayered personnel policies to keep untrustworthy individuals from government jobs that involve handling classified information. They invest heavily in complex information systems to block access to sensitive communications.
Beyond Breaches: The Spectrum of Costs from Espionage and Pre-Positioning
What are the costs of cyber espionage? And how do they differ from those of operations designed to prepare for attack?
Unpacking State-Sponsored Cyber Conflict: Intelligence-Driven Strategic Competition in Cyberspace
In 2010, Stuxnet, a stealthy, sophisticated computer worm widely attributed to the United States and Israel, infiltrated Iran’s Natanz uranium enrichment facility and sabotaged its industrial controls, delaying Iran’s nuclear program without a single bombing raid or overt military strike. A few years later, Russian operatives hacked into U.S. political organizations in 2016, stealing and leaking emails in an effort to sway the presidential election. At the same time, Chinese state-sponsored groups quietly penetrated foreign government and corporate networks to siphon off military technology and industrial secrets over many years. These incidents, though bloodless and often deniable, had clear strategic stakes.

State-Sponsored Cyber Conflict: How Russia Responds to Election Interference Allegations on Social Media
Russia has been repeatedly accused of employing non-state cyber proxies to conduct sophisticated cyber-attacks and information operations aimed at influencing US elections. These allegations, notably around the contentious 2016 US presidential election, have attracted substantial global attention, underscoring critical vulnerabilities within democratic institutions.

Insuring the Unseen: Closing the Protection Gap in Economic Cyber-Espionage
Economic cyber espionage represents an ongoing threat to both nations and markets, yet unlike other cyber threats, it remains largely uninsured. This does not have to be the case. The underinsurance for economic cyber espionage is more of a mechanical problem, with coverage gaps hinging on proving damage to intangible assets. In fact, this protection gap persists even when attackers are “incompetent” (i.e., unable to use the IP they steal), since victims still incur measurable, indemnifiable costs.

Buying Security: Open Source Software Funding and Security Posture
The security of open source software (OSS) has morphed from a niche technical concern to a central cybersecurity policy challenge. High-profile incidents have led to suggestions for governments to help strengthen the OSS ecosystem, including calls for funds built to support open source projects and their maintainers, such as a proposal for an EU Sovereign Tech Fund. This research examines the argument that unconditional funding—namely, financial support without specific requirements for the recipient—causally improves the security posture of OSS projects.
Artificial Intelligence & Language Preservation
The United Nations Educational Scientific and Cultural Organization (UNESCO) has designated 2022-2032 the International Decade of Indigenous Languages. This initiative comes at a time when endangered language speakers, linguists, and other groups are concerned about language extinction and the rapid spread of artificial intelligence (AI). Some researchers are optimistic that AI can be leveraged to help document, preserve, and revitalize at-risk languages, while others are concerned that the technology will accelerate the homogenization of human language.
Blocking exports and raising tariffs is a bad defense against industrial cyber espionage, study shows
Supply-chain decoupling doesn’t stop rival nations from hacking each other and can make it worse. A cyber-espionage expert explains what does work.

True Costs of Misinformation | The Global Spread of Misinformation Laws
Between 2010 and 2022, 80 countries enacted new legislation or amended existing laws in an attempt to curb the spread of misinformation online. This sharp and global adoption of misinformation laws, however, cannot be explained by the sudden emergence of false or misleading information, as these problems have existed for a very long time.

Creating and Implementing a Liability Regime for Software Vendors
Insecure software is a national security risk, costs the U.S. billions of dollars annually, and exposes users’ information to malicious actors. Software developers (vendors) who fail to securely develop their products currently face few legal repercussions, even if they engage in industry-agreed bad practices.

Gotta Track’em All: Data Privacy and Saudi Arabia’s Pokémon Go Acquisition
In a given month, more than 100 million people open Pokémon Go—the app that allows users to superimpose the world’s most profitable media franchise onto reality using only their smartphone. Using their phone camera and a flick of the wrist, they captured tiny digital monsters at the park, at the office, sometimes in active minefields, and, yes, in the bathroom.
Who else was watching?

Primer on the Costs of Cyber Espionage
Cyber espionage is the use of cyber tools and techniques to gather intelligence or steal sensitive information from targeted entities. This form of espionage poses significant risks to national security, economic stability and corporate integrity. Given the complex and often hidden nature of cyber espionage activities, accurately measuring their costs presents a significant challenge.

Strategic Authoritarian Narratives in the Sahel
In recent years, countries in the Sahel region of Africa have faced widespread insecurity and instability. Stretching across the northern tier of sub-Saharan Africa, Sahel countries Niger, Mali, and Burkina Faso have all experienced a series of military coups and rising levels of right-wing extremism.

Technical infrastructure as a hidden terrain of disinformation
While social media disinformation has received significant academic and policy attention, more consequential forms of intentional manipulation target the underlying digital infrastructures upon which society depends.

Disinformation and Identity-Based Violence
Disinformation spread via digital technologies is accelerating and exacerbating violence globally. There is an urgency to understand how coordinated disinformation campaigns rely on identity-based disinformation that weaponizes racism, sexism, and xenophobia to incite violence against individuals and marginalized communities, stifle social movements, and silence the press.

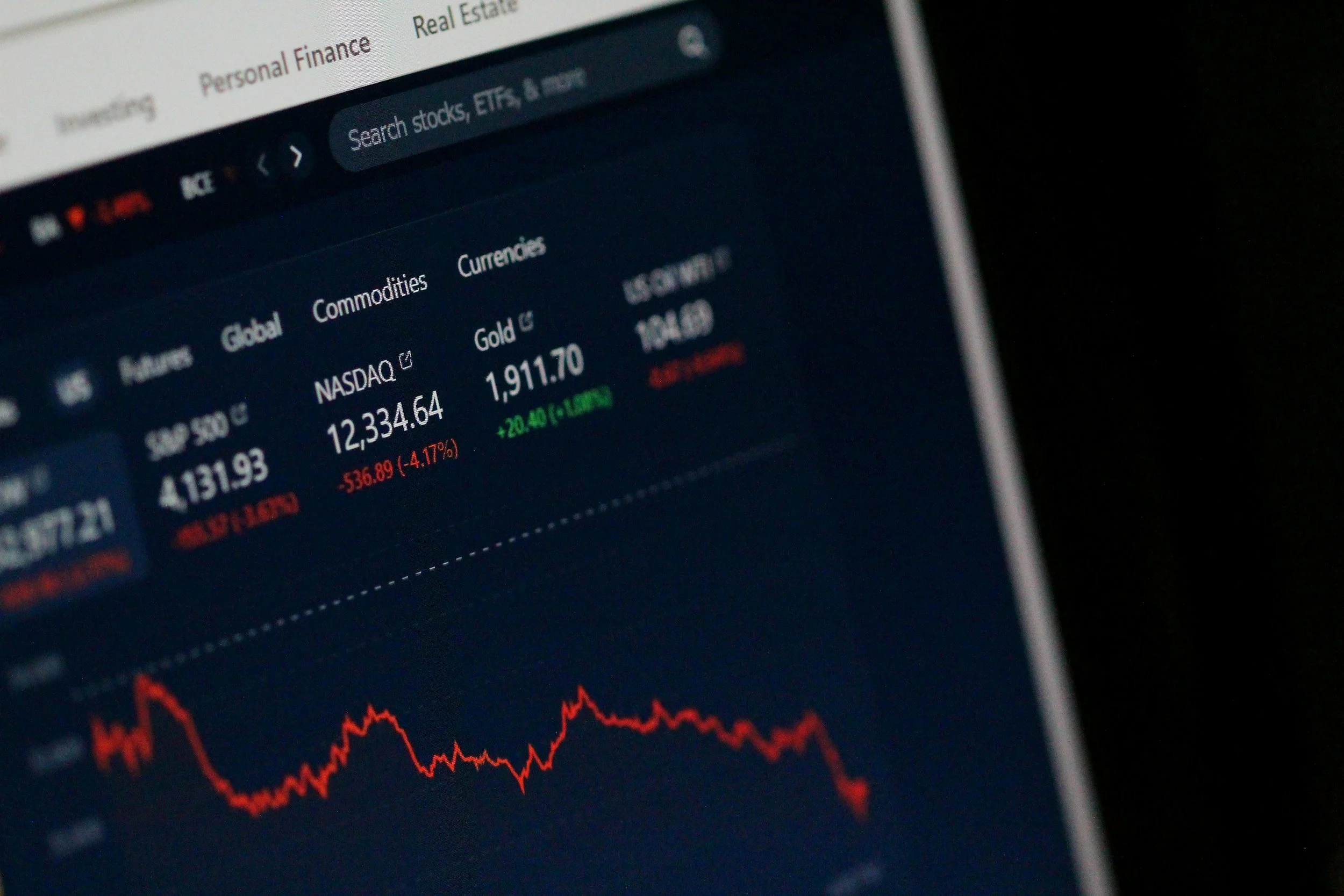
State-sponsored cyber attacks and co-movements in stock market returns: evidence from US cybersecurity defense contractors
As cyber threats become increasingly central to international politics, state-sponsored cyber attacks have become an instrument of geopolitical leverage.

Exporting Autocracy: How Foreign Influence Operations Shape Democratic Attitudes
What impact do foreign authoritarian influence operations (FIOs) have on democracy? Through an examination of democratic attitudes in 15 African countries between 2009 and 2023, we present preliminary but compelling evidence that autocrats export authoritarianism.

Misinformed about Misinformation: On the polarizing discourse on misinformation and its consequences for the field
For almost a decade, the study of misinformation has taken priority among policy circles, political elites, academic institutions, non-profit organizations, and the media.

Mythical Beasts and Where to Find Them
The Mythical Beasts project addresses this meaningful gap in contemporary public analysis on spyware proliferation, pulling back the curtain on the connections between 435 entities across forty-two countries in the global spyware market. These vendors exist in a web of relationships with investors, holding companies, partners, and individuals often domiciled in different jurisdictions.
